Sometimes, applications have client-side input validation mechanisms through JavaScript, hidden forms, or POST parameters that one doesn't know or can't see or manipulate directly in the address bar; to test these and other kind of variables, we need to intercept the requests the browser sends and modify them before they reach the server. In this recipe, we will use a Firefox add-on called Tamper Data to intercept the submission of a form and alter some values before it leaves our computer.
- Go to Mantra's menu and navigate to Tools | Application Auditing | Tamper Data.
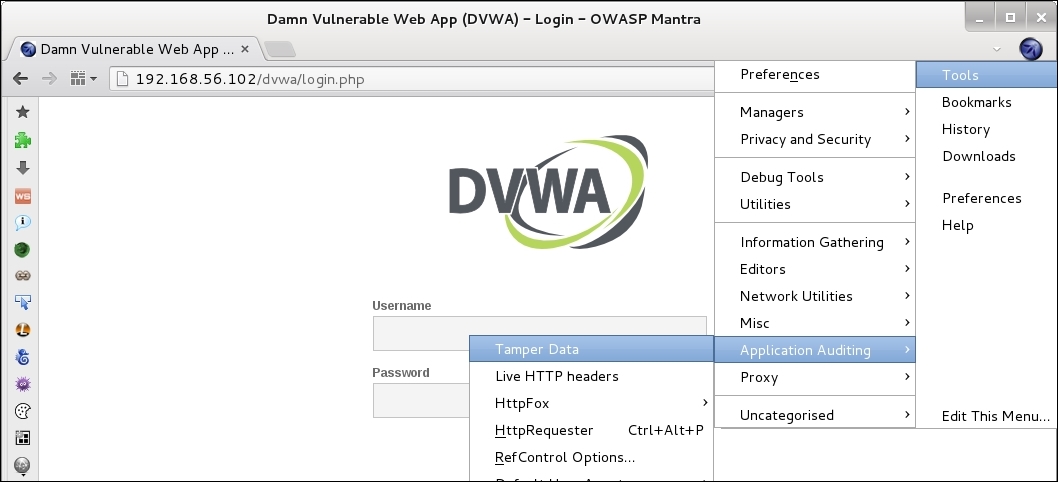
- Tamper Data's window will appear. Now, let's browse to
http://192.168.56.102/dvwa/login.php. We can see the requests section in the add-on populating: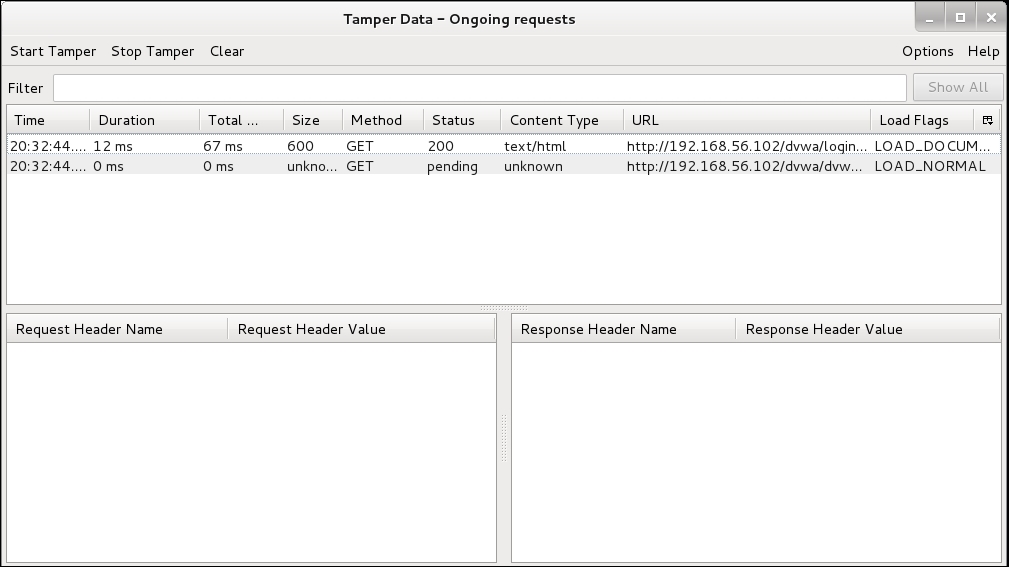
- To intercept a request and change its values, we need to start the tampering by clicking on Start Tamper. Start the tampering now.
- Introduce some fake username/password combination; for example,
test/passwordand then click on Login. - In the confirmation box, uncheck the Continue Tampering? box and click Tamper; the Tamper Popup window will be shown.
- In this pop-up, we can modify the information sent to the server including the request's header and POST parameters. Change username and password for the valid ones (
admin/admin) and click on OK. This should be used in this book instead of DVWA: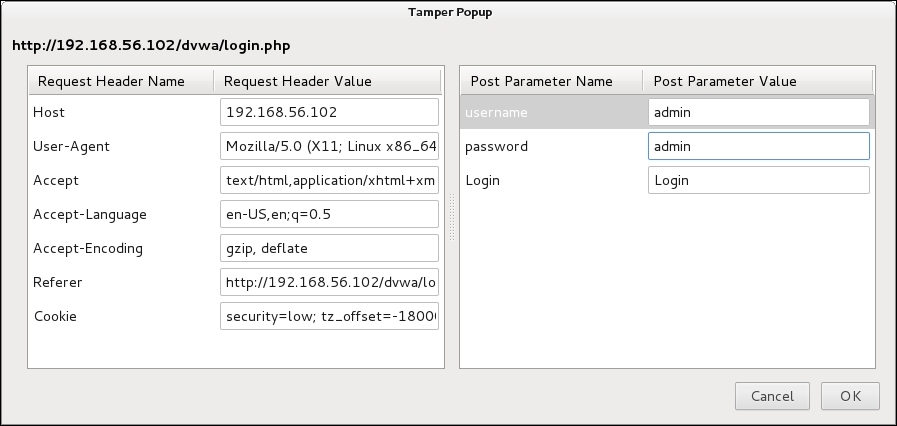
With this last step, we modified the values in the form right after they are sent by the browser. Thus, allowing us to login with valid credentials instead of sending the wrong ones to the server.